For security reasons you may want to introduce account locking, where after a set number of incorrect passwords users cannot log into their accounts even when they have the correct password. This can prevent brute force password attacks. Foreman allows admins to pick the account lock number from 1 to 5, or none (default). This is available in the “User & Account Options” Tab in “Administration”:

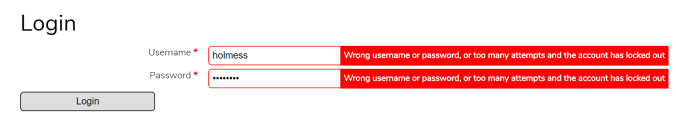
This is what a user would see when they are locked out:
Admins can unlock users in the “Validate, Reset, & Deactivate Users” tab in “Administration”. Note that the number of locked users is highlighted in the tab title in red:

If there are users locked out, and the admin changes the account lock setting from X attempts to No lockout, they are all automatically unlocked.









 Please
Please 

